try debugging or reversing in ida? btw which cf x32 or x64? i have a pattern here
Thread: how to get this addres
Results 1 to 13 of 13
-
01-22-2021 #1
 how to get this addres
how to get this addres
hello guys how to get this address in IDA Pro
#define aLTClientShell
#define aLTModel 0
#define dwCPlayerStart
#define dwCPlayerSize
#define MEOffset
#define aIntersectSegment

Last edited by antierror; 01-23-2021 at 01:14 AM.
-
01-22-2021 #2
-
01-22-2021 #3
-
01-22-2021 #4
-
01-22-2021 #5
-
01-23-2021 #6
-
01-23-2021 #7
bruhhh those thing doesn't have string XD
here is the pattern
Code:NetVars::get()->Pointer.m_LTClientShell = NetVarManager::get()->GetOffset(xorstr_(_T("m_LTClientShell")), eCShell, (BYTE*)"\x8B\x0D\x00\x00\x00\x00\x3A\xC3\x6A\x00\x68\x00\x00\x00\x00\x8D\x45\xEC", "xx????xxxxx????xxx", 2); NetVars::get()->Pointer.m_LTModel = NetVarManager::get()->GetOffset(xorstr_(_T("m_LTModel")), eCShell, (BYTE*)"\x8B\x0D\x00\x00\x00\x00\x50\xFF\x56\x00\x85\xC0\x75\x70", "xx????xxx?xxxx", 2); NetVars::get()->Offset.m_PlayerStart = NetVarManager::get()->GetOffset(xorstr_(_T("m_PlayerStart")), eCShell, (BYTE*)"\x0F\xB6\x86\xFC\x01\x00\x00\x69\xC0\x00\x00\x00\x00\x8A\x84\x30\x04\x02\x00\x00", "xxxxxxxxx????xxxxxxx", 3); NetVars::get()->Offset.m_PlayerSize = NetVarManager::get()->GetOffset(xorstr_(_T("m_PlayerSize")), eCShell, (BYTE*)"\x69\xC0\x00\x00\x00\x00\x8A\x84\x30\x04\x02\x00\x00\x5E", "xx????xxxxxxxx", 2); NetVars::get()->Offset.m_LocalIndex = NetVarManager::get()->GetOffset(xorstr_(_T("m_LocalIndex")), eCShell, (BYTE*)"\x8A\x84\x30\x04\x02\x00\x00\x5E", "xxxxxxxx", 3); NetVars::get()->Expression.m_IntersectSegmentVT = NetVarManager::get()->GetAddress(xorstr_(_T("m_IntersectSegmentVT")), eCF, (BYTE*)"\x55\x8B\xEC\x8B\x45\x0C\x50\x8B\x4D\x08\x51\x8B\x15\x00\x00\x00\x00", "xxxxxxxxxxxxx????");
-
01-23-2021 #8
If you're reversing 64bit version you can simply search string "ILTClient.Default" then look for the second xref.

The BaseAddress on my screenshot is the Address you're looking for then you can use reclass to find the class instances under the BaseAddress.
#define dwCPlayerStart
#define dwCPlayerSize
#define MEOffset
These offsets are under CLTClientShell which can be found under the BaseAddress to get the dwCPlayerSize you can just subtract the next Player's ModelInstance to the first ModelInstance in the CLTClientShell. The dwCPlayerStart would be obviously the first ModelInstance in the CLTClientShell. The MeOffset is the offset above the ModelInstance.
The aIntersectSegment is a virtual function you can just call it without hard-coding the address simply walk the ICLTClient vtable and use the correct vtable index.
-
01-23-2021 #9
-
01-23-2021 #10
Teleport is already closed in 1 month in cf west 20_0 become not working for west

about fast knive have As such, there is a way that does not cause 14_0
and bypass 14_0 is already shared
- - - Updated - - -
aboutCode:LTClientShell = 8B 0D ?? ?? ?? ?? 3A C3 6A ?? 68 ?? ?? ?? ?? 8D 45 EB + 0x2 aLTModel = 8B 0D ?? ?? ?? ?? 50 FF 56 34 85 C0 75 70 aIntersectSegment = 5D C3 CC CC CC CC CC CC CC CC CC CC CC CC CC 55 8B EC 8B 45 0C 50 8B 4D 08 + 0xF
it's all update same not changedCode:#define dwCPlayerStart #define dwCPlayerSize #define MEOffset
Click Alt + B and add it's pattern you get address
after get that open Hex Calculator and past address
see up in ida iambase: copy that and Shortage address
i want in lord you understand
Enjoy
Last edited by Anger5K; 01-23-2021 at 08:38 AM.
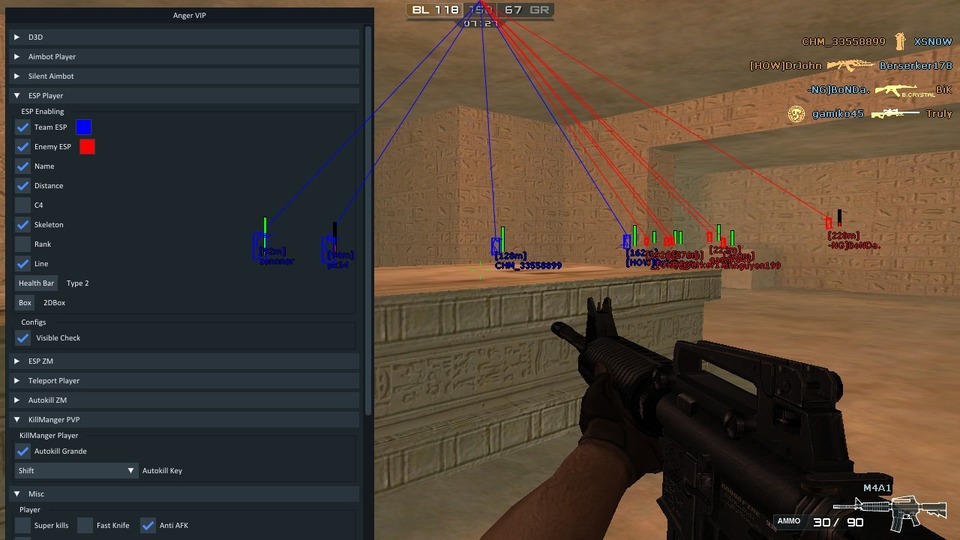
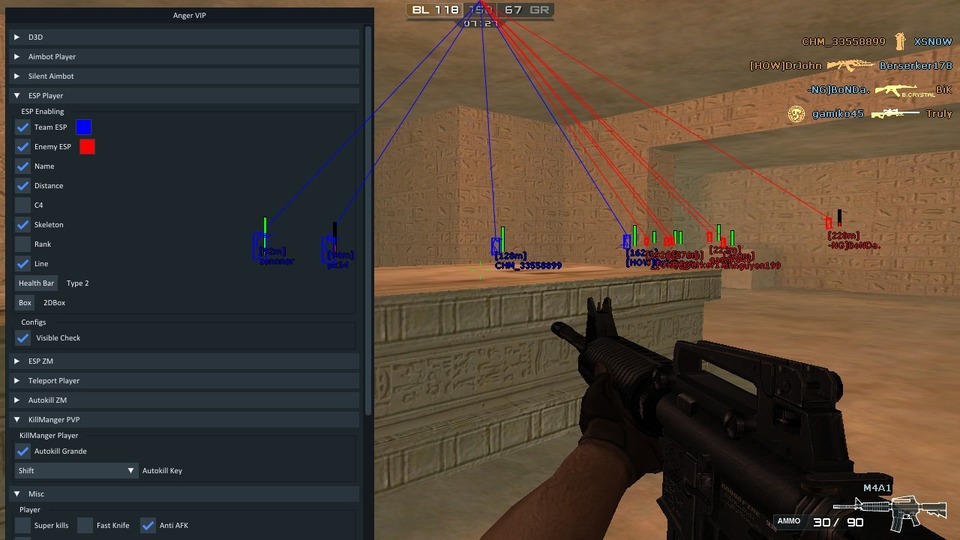
My Own Hack!!!


-
The Following User Says Thank You to Anger5K For This Useful Post:
antierror (01-23-2021)
-
01-23-2021 #11
Thank you very much, anger, I got the addresses
-
01-23-2021 #12
thanks lord for your understand
 My Own Hack!!!
My Own Hack!!!


-
01-23-2021 #13
Similar Threads
-
how to get this
By Symmetrical Jr in forum GeneralReplies: 17Last Post: 04-04-2013, 02:24 PM -
[Request] How to get this FoV ?
By KillTheHack in forum Call of Duty Modern Warfare 3 DiscussionsReplies: 7Last Post: 10-26-2012, 11:23 PM -
How to get this stuff?
By renmoo in forum Alliance of Valiant Arms (AVA) DiscussionsReplies: 2Last Post: 06-28-2011, 12:09 PM -
How to get this hack working for vista (32 and 64) and windows 7
By 12pollej in forum Combat Arms HelpReplies: 7Last Post: 05-04-2010, 09:27 PM -
how you get this gun
By Danyo in forum CrossFire DiscussionsReplies: 4Last Post: 04-08-2010, 07:23 AM


 General
General






 Reply With Quote
Reply With Quote








